輸入(低→高)
- マルウェアが機密ネットワークに侵入するのを防ぎます。
- Multiscanning、Adaptive Sandbox 、Deep CDR™ テクノロジー、一方向制御、およびプロトコルブレークを組み合わせています。
OPSWAT Solutionsは、信頼度や機密レベルが異なるネットワーク間でデータを安全にやり取りするための、モジュール式のクロスドメイン・セキュリティ・ソリューションです。MetaDefender として構築されており、高度な脅威防止機能、データダイオード、セキュリティゲートウェイを統合することで、データのインポートおよびエクスポート制御を徹底し、マルウェアやデータ漏洩を防止するとともに、防衛、情報機関、重要インフラ環境におけるコンプライアンスに準拠したワークフローを支援します。


日常的なユーザーファイルから、地理空間データ、インストーラー、アプリケーションのアップデートに至るまで、ドメインをまたいで移動するデータは現在、大量かつ多様なフォーマットで提供されている。レガシーシステムやハードウェアのみのシステムでは、このような多種多様なデータの処理に苦戦し、柔軟で拡張可能な方法で必要なセキュリティ強化機能(SEF)を提供するための拡張性がありません。
システムは、国家の脅威を含む、非常に機知に富んだ攻撃者に耐えなければならない。セキュリティ・レベル間のデータ転送は、従来の防御では対処できない脆弱性を露呈し、AI主導の攻撃は最新の適応型防御を要求する。

データを永続的に分離することは、もはや領域を超えたコラボレーションのニーズを満たすことはできません。最新のCDSシステムは、API APIクラウドからオンプレムへのシームレスな転送を可能にしながら、多様なボリューム、データタイプ、アプリケーションをサポートし、ビジネスの要求に適応しなければなりません。
OPSWAT 、既存のプロセスに追加するモジュール式のソフトウェア主導型アプローチを提供し、市場をリードするテクノロジーで
。
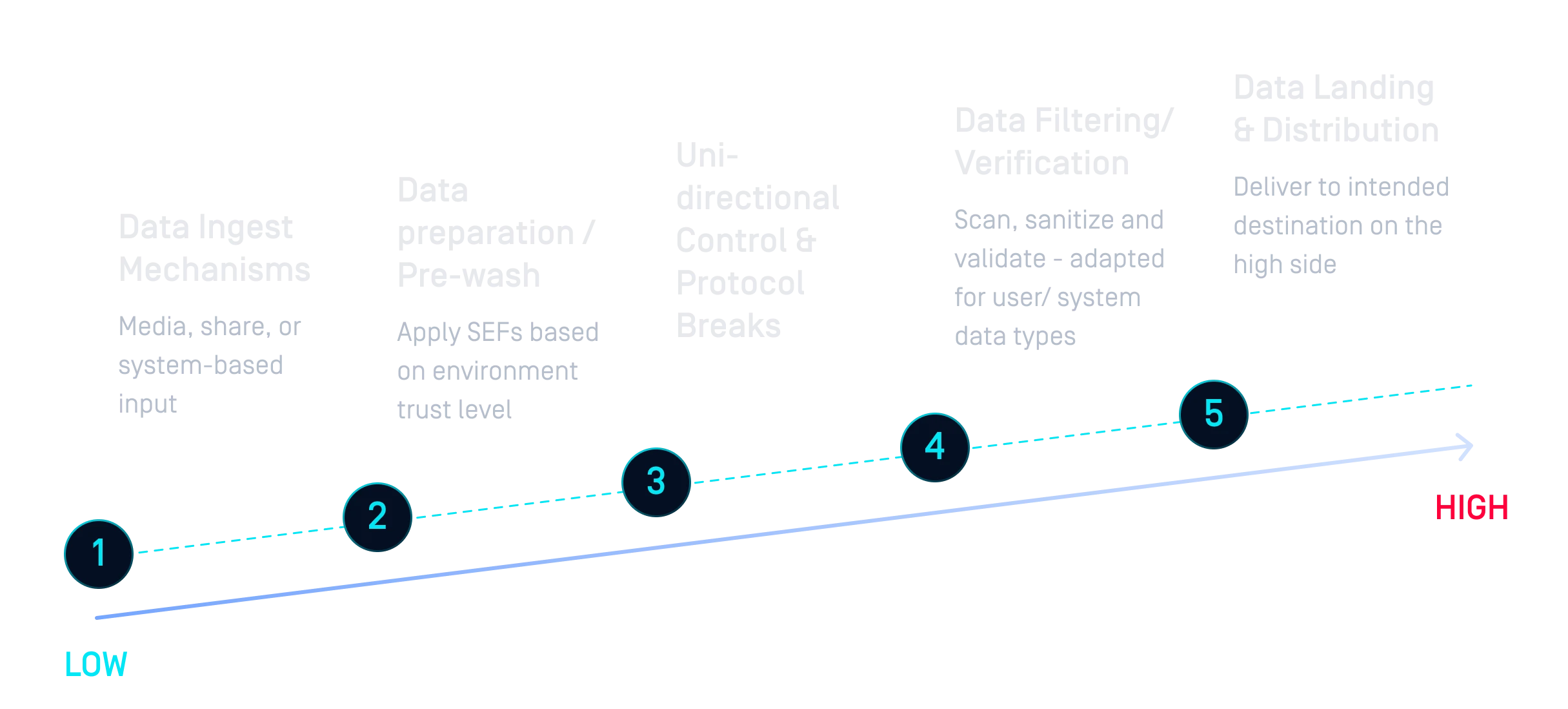
市場をリードするテクノロジーとプラグイン/プラグアウト機能を備えたOPSWATモジュラー・アプローチは、CDSソリューションをより効率的に構築する方法です。
エミュレーション・サンドボックスにより、企業はOSパッチやアプリケーションのような複雑なデータタイプのIOCを調べ、潜在的な脅威ベクトルを排除することができる。
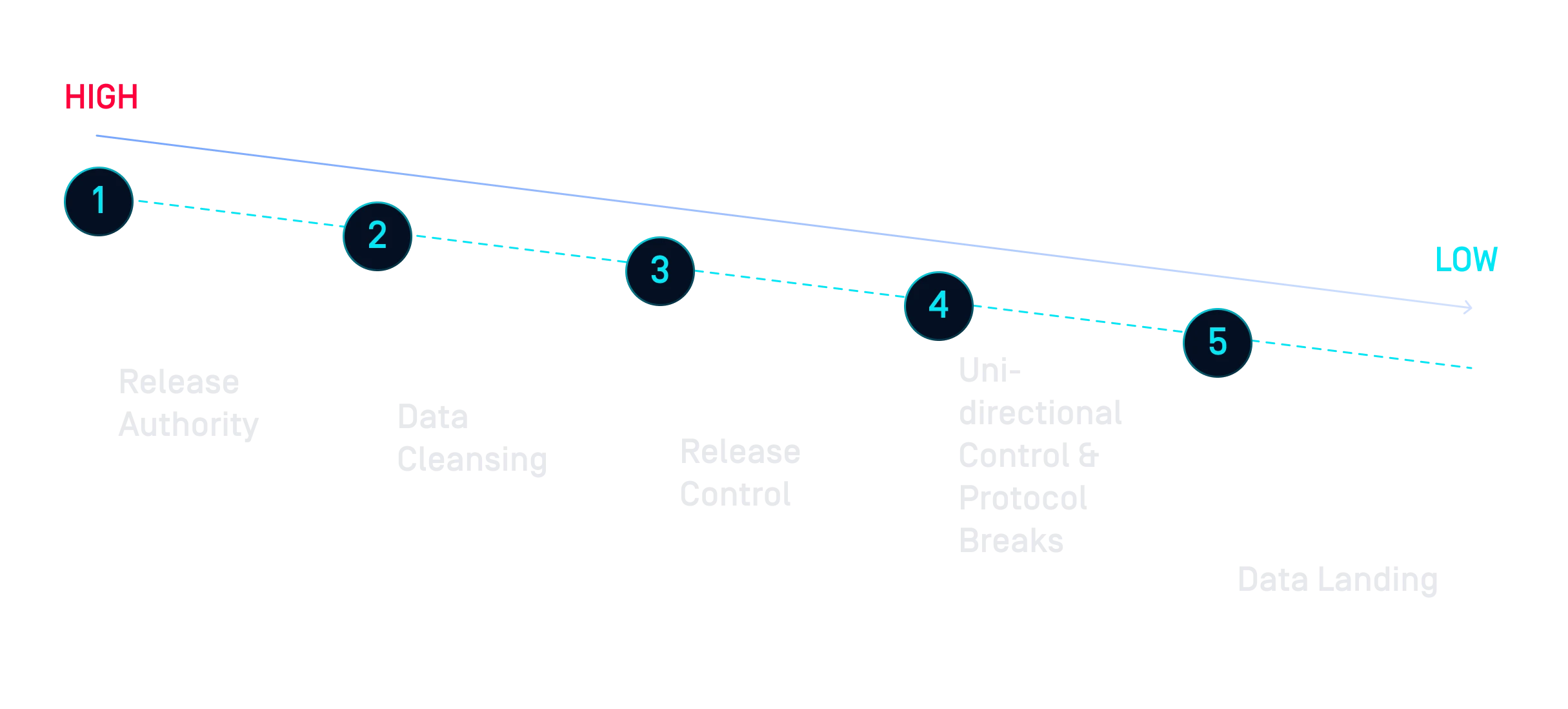
Proactive DLP 、ファイル内の機密情報を検出してブロックすることで、(パートナーと共有するレポートなど)上位分類から下位分類に転送されるデータに、公開を意図しない機密情報が含まれていないことを保証するのに役立ちます。
MetaDefender Kiosk使えば、Media データは、組織のリスク態勢に基づいて適切なセキュリティ実施メカニズムを通過することができます。
主な利点の1つは、MFT ようなツールと組み合わせてMDCore 使用することで、完全な監査証跡を残すことができ、組織はどの役割またはペルソナがデータを流出させようとしたかを追跡して確認することができます。
データを分離し、コラボレーションを困難にする従来のエアギャップ方式とは異なり、OPSWATソリューションはクロスドメインアーキテクチャに統合され、セキュリティポリシーを実施します。ハードウェアとソフトウェアのハイブリッドアプローチは、機密データが適切に管理、監視、監査されることを保証しながら、複数の利害関係者のコミュニティをサポートします。
サイバー攻撃とそれを実行する脅威者がより巧妙になるにつれ、世界中の統治機関は、重要なインフラが安全であり続けるために必要なことを確実に行うための規制を実施している。