重要インフラに関するCAF 4.0の主な変更点と新たな要件とは何ですか?
CAF(サイバー評価フレームワーク)は、重要サービスを提供する組織がサイバーリスクとレジリエンスをどのように管理しているかを評価するための、英国の国家モデルです。2025年に英国NCSC(国家サイバーセキュリティセンター)によって発表されたCAF 4.0は、チェックリストによる審査に代わり、重要インフラに対する測定可能で成果ベースのレジリエンスを重視することで、より高い水準が求められるようになりました。
主な更新点
- 社内システムおよびサプライヤーシステムにおけるSecure 開発およびライフサイクル管理Secure (A4.b)
- 安全でない、または意図しないシステム動作を防ぐためのAIおよび自動化のリスク管理
- 原則C2における必須機能としての能動的な脅威ハンティング
- サプライチェーンの保証と下請け業者の可視化
- エネルギー、医療、交通、デジタルインフラの各分野におけるニーズに合わせたセクター別オーバーレイ
- 脅威の理解(A2.b)への明確な重点と、IGP(優良事例指標)を通じたセキュリティの検証
NIS2(EUの改定版ネットワーク・情報システム規制)および英国のレジリエンス法案に準拠したCAF 4.0は、取締役会レベルの説明責任を強化するとともに、目標A~Dに基づくガバナンスと改善の継続的な実証を義務付けています。
CAF 4.0は以前のバージョンとどう違うのですか?
NCSCが開発したCAF 4.0は、単なるチェックリストの遵守にとどまらず、測定可能な成果と継続的な改善を目指しています。このバージョンでは、セクター固有のオーバーレイによって裏付けられた、「脅威ハンティング(C2)」や「Secure Software (A4.b)」といった新たな原則が導入されています。
主な違い
- 成果に基づく証拠がチェックリストに取って代わり、各原則を満たす上で組織に柔軟性をもたらす
- IGPは、厳格な採点ではなく、専門家の判断を導くものである
- 脅威ハンティング(C2)およびセキュアなソフトウェア開発(A4.b)に関する新たな指針
- 業界別のオーバーレイに対応しており、規制当局は各業界に合わせて期待値を調整できる
- ガバナンスと保証への注力をさらに強化し、取締役会レベルでの主体的な取り組みを求める
実際には、CAF 4.0 では、検証可能な証拠と文書化された脅威ハンティングの手順が求められます。以前のバージョンではネットワーク監視が重視されていましたが、4.0 では、積極的な脅威ハンティングと検証済みの結果を要求する、専用の「脅威ハンティング」原則が追加されています。
CAF 4.0における一般的な課題と、フレームワークによる解決策
| 課題 | CAF 4.0 ではどのように対応しているか |
|---|---|
| 複雑で重複する規制要件への対応 | CAF 4.0は、NIS2指令および英国のレジリエンス法案に準拠しており、セクター横断的なガバナンス、保証、およびレジリエンスのための統一モデルを構築しています。 |
| 継続的な証拠収集と脅威の監視を行うためのリソースが限られている | CAF 4.0では、チェックリスト形式の監査に代わり、成果に基づく証拠と継続的な評価が採用されており、組織はより効率的にコンプライアンスを証明できるようになります。 |
| セキュア開発やAIリスクに関する新たな指針をどのように実践に移すべきか、その方法について不透明感がある | CAF 4.0では、Secure Software [A4.b]およびAIリスク管理に関する明確な原則が導入され、ライフサイクル管理、テスト、およびプロヴェナンスについて体系的な指針が示されています。 |
| ボード向けコンプライアンスおよびレジリエンス報告書の作成が困難である | CAF 4.0は、測定可能な目標とIGP(優良事例指標)を通じて経営陣の説明責任を強化し、取締役会への報告をより一貫性のある、データに基づいたものとしています。 |
CAF 4.0では、AIのリスクとSecure 最優先事項となっている
CAF 4.0では、AIを活用した自動化や複雑なソフトウェア・サプライチェーンが新たなリスクを生み出し、その開発や管理が適切に行われない場合、重要なサービスに支障をきたす可能性があることを認識しています。
組織に対する要件
- ソフトウェアのライフサイクル全体を通じて、コードの出所追跡、テスト、脆弱性管理などのセキュア開発手法を適用する
- 予測不能な動作をしたり、攻撃者に悪用されたりする可能性のある、AI駆動型または自動化された意思決定システムによるリスクを評価し、管理する
- セキュア開発基準を遵守させるサプライヤー保証プロセスを通じて、ソフトウェアおよびアップデートの真正性と完全性を確認する
これらの更新により、セキュア開発とAIリスク管理が体系化され、重要なシステムへの展開前に脆弱性を排除するとともに、NIS2指令および英国のレジリエンス法案に準拠します。
新しいセクター・オーバーレイとセキュリティリーダーへの影響
CAF 4.0では、必須サービスを提供する業界において本フレームワークを実用的なものとするため、業種別のCAFプロファイル(オーバーレイ)が導入されました。NCSCの指導の下で開発されたこれらのオーバーレイにより、CAFは共通の国家フレームワークとしての性格を維持しつつ、業種に応じた解釈が可能となります。
オーバーレイは、各セクターの業務上の実情に合わせて同じ枠組みを適応させる、いわば「オーダーメイドの設計図」と考えてください。各オーバーレイは、CAFの成果を、そのセクター特有のリスク、技術、規制上の期待に合わせて調整するものです。
セクター・オーバーレイの主な目的
- 業界別の解釈:エネルギー、医療、運輸、およびデジタルインフラの事業者が、それぞれの事業環境においてCAFの原則を適用できるようにする
- 規制の整合化:規制当局が、実際の運用状況を反映したレジリエンス目標を設定できるようにする
- リーダーシップの重点:セキュリティ責任者が、自らの重要な職務において最も重要な成果に集中できるよう支援する
- 一貫性のある測定:IT環境とOT環境全体におけるサイバー成熟度の統一的な評価を支援する
経営陣にとって、これらのオーバーレイは各領域における「理想的な状態」を明確にし、CAF 4.0を単なるチェックリストではなく、リスクとエビデンスの優先順位付けを行うための実用的なツールへと変えるものです。
OPSWAT 、CAF 4.0への準拠を簡素化し、運用化します
OPSWAT CAF 4.0の成果指標と整合しており、フレームワークの目標をITおよびOT環境全体にわたる測定可能な運用管理策へと具体化します。
主な連携分野
- CAFの目標B(サイバー攻撃からの防御)および目標C(サイバーセキュリティ事象の検知)に沿った脅威の防止と検知。機械学習と行動分析を活用したC2脅威ハンティングのため、MetaDefender およびMetaDefender によってサポートされています。
- MetaDefender Core における SBOM 生成と脆弱性スキャンによるSecure 検証は、ソフトウェアの完全性について測定可能な保証Core
- 自動化されたレポートにより、可視性が確保され、監査対応が容易になります
- 分離されたネットワーク間のドメインをまたぐ安全なファイル交換は、データフローの保護に役立ちます
CAFに準拠したコンプライアンス・マッピングにより、OPSWAT セキュリティチームが単なるチェックリスト形式のコンプライアンスを超え、継続的な保証と測定可能なレジリエンスを実現できるようOPSWAT 。以下の表は、OPSWATテクノロジーがCAFの目標とどのように対応しているかを示しており、組織が測定可能で証拠に基づいたコンプライアンスを実証するのに役立ちます。
OPSWAT 、組織がCAF 4.0の課題に対処するのをどのように支援するか
| 課題 | OPSWAT |
|---|---|
| 複雑で重複する規制要件への対応 | OPSWATコンプライアンス・マッピング機能OPSWAT、CAF 4.0、NIS2、および英国レジリエンス法案を単一の 報告フレームワークに統合します。目標と管理措置の自動照合により、 個別の監査の必要性が軽減されます。 |
| 継続的な証拠収集と脅威の監視を行うためのリソースが限られている | MetaDefender Core、MetaDefender Managed File Transfer、My OPSWAT Central Management は、ログ、監査証跡、および制御ステータスデータを自動的に収集します。これらの機能により、 手動での追跡作業を必要とせずに、継続的な証拠を提供します。 |
| セキュア開発とAIリスク管理をどのように実践すべきかについての不確実性 | MetaDefender Core 、ソフトウェアの真正性をCore 、SBOMを生成し、脆弱性データを管理します。 一方、Sandbox を活用した動作分析Sandbox 、デプロイ前に安全でないコードや改ざんされたコードを特定します。 |
| ボード向けコンプライアンスおよびレジリエンス報告書の作成が困難である | OPSWAT集中管理されたコンプライアンスビューとレポート機能により、技術的な証拠が、CAFの目標A~Dに対応した経営層向けの 要約へと変換されます。これにより、経営陣はコンプライアンスの 成熟度とリスク態勢を明確に把握できるようになります。 |
OPSWAT 、CAF 4.0 に向けた証拠に基づくコンプライアンスOPSWAT
OPSWAT自動的な証拠収集機能、一元化されたコンプライアンス状況の可視化、およびデータポイントとCAF目標とのリアルタイムなマッピングを活用することで、CAF 4.0の報告業務を効率化できます。これらのCAF 4.0への対応策は、重要インフラ環境におけるOPSWAT において、すでに実践されています。
CAFの継続的な保証を支えるOPSWAT 主要OPSWAT
- SBOMの生成vulnerability detection、CAF A4.bに基づくセキュア開発の実践を直接的に証明するものであり、技術的な証拠をOPSWAT 結びつけるものです。
- MetaDefender Core MetaDefender File Transfer™の監査レポートは、CAFの目標AおよびDに対応しており、CISOに対し、コンプライアンスの進捗状況を証明する、追跡可能で規制当局への提出に耐えうる要約情報を提供します
OPSWAT テクノロジーの主な機能
CAFの目標に対するコンプライアンス状況をリアルタイムで可視化する一元化されたコンプライアンスビュー
継続的な証拠収集を支援するログ、レポート、および監査証跡の自動収集
監督者による承認ワークフローおよび詳細な監査ログにより、CAF目標D2に沿って、ファイルの移動、ポリシーの適用、および人的監督が記録されます
ロジックに基づくフィルタリングと定期的な再スキャンにより、新たな脅威や新興の脅威に対するコンプライアンス検証が自動化され、CAFの継続的レビュー要件をさらに支援します
データの完全性を検証するために、セキュアなファイル転送、アクセス制御、および脅威分析ツールと連携する
OPSWATドメイン対応OPSWAT、OT Security他社と一線を画す理由は何か?
CAF 4.0では、重要機能を支えるITシステムとOTシステム全体にわたる統合的なセキュリティ対策が求められています。OPSWAT統合プラットフォームは、データフロー、デバイス、ネットワークが交差するあらゆる箇所を保護します。このアプローチは、エネルギー、運輸、デジタルインフラといった分野におけるCAFのセクター別要件に対応するものであり、これらの分野では、ITシステムとOTシステム全体にわたる統合的な可視性が規制上の要件としてますます重要視されています。
一部のベンダーがOTの可視化やITベースの監視に限定して注力している一方で、OPSWATCAF準拠プラットフォームは、単一のセキュリティおよびコンプライアンスモデルのもとで、両方の領域を保護します。
Core
- ITシステムとOTシステムの統合的な保護
MetaDefender Core、MetaDefender Managed File Transfer、MetaDefender 、MetaDefender などの技術を組み合わせ、接続環境およびエアギャップ環境を問わず、ファイルのやり取りとエンドポイントを保護します
- Secureポリシーに基づいたファイル転送
MetaDefender Managed File Transfer 、ワークフロールール、承認プロセス、監査ログを活用してネットワーク間のファイル転送Managed File Transfer 、コンプライアンスとデータの完全性を確保します
- 起動前のMultiscanningによるデバイスの信頼性確保
MetaDefender Drive 、エンドポイントがネットワークにFile-Based Vulnerability Assessment ベアメタル環境Multiscanning File-Based Vulnerability Assessment Drive 、マルウェアの拡散を防ぐのに役立ちます
- リムーバブルメディアのMedia
MetaDefender Kiosk 、Proactive DLP™およびセキュア消去機能Kiosk 、リムーバブルメディアがセキュアな環境に入る前にその内容を検証・消去します
- 一元化された可視化とレポート機能
MetaDefender Core、Managed File Transfer、My Central Management 、管理対象環境全体におけるデバイス、ユーザー、およびファイルのアクティビティを表示する統合ダッシュボード、SIEM連携機能、および監査ログCentral Management
OPSWATでは、高度な脅威ハンティングとAIによるリスク対策がどのように行われているのでしょうか?
OPSWAT 、MetaDefender 、MetaDefender Intelligence™、Coreを通じて、隠れた脅威OPSWAT 、AIを活用したソフトウェアの動作を検証することで、NCSCの「サイバー評価フレームワーク4.0(CAF 4.0)」における目標C2およびB4.aを満たしています。
OPSWAT Core OPSWAT
- Metascan™Multiscanning リアルタイム脅威インテリジェンス:ファイルのやり取りやデバイス全体にわたる高度な脅威やゼロデイ脅威を検知
- Sandbox : 既知のインジケーターがなくても悪意のある動作を検知し 、構造化された証拠を得るためにMITRE ATT&CK(敵対的戦術、技術、および共通知識)マッピングを通じて結果を関連付けます
- AIを活用した分析: 自動化された意思決定の妥当性を検証し 、システム動作における異常を検知する
- これらの技術に対する継続的な更新: 進化するCAF 4.0の要件に適合する
これらの機能を組み合わせることで、既知の脅威と新たな脅威の両方に対して高い検知精度を実現するとともに、CAF評価のための検証可能な証拠を提供します。
以下の表は、OPSWATテクノロジーが「サイバーアセスメントフレームワーク(CAF)4.0」の目標および原則とどのように整合しているかをまとめたものであり、各製品がITおよびOT環境全体において、測定可能かつ証拠に基づいたコンプライアンスの実現にどのように貢献しているかを示しています。
CAF 4.0の目標および原則OPSWAT 機能
| OPSWAT | 主な特徴 | CAF 4.0 で扱われる目標/原則 | この機能がCAF 4.0への準拠をどのようにサポートするか |
|---|---|---|---|
| MetaDefender コア |
|
|
|
| MetaDefender |
|
|
|
| MetaDefender Intelligence™ |
|
|
|
| MetaDefender Managed File Transfer™ (MetaDefender マネージド ファイル トランスファー |
|
|
|
| MetaDefender Kiosk™ |
|
|
|
| MetaDefender ドライブ |
|
|
|
| MetaDefender |
|
|
|
| MetaDefender ネットウォール |
|
|
|
| My Central Management |
|
|
|
セキュアな開発やサプライチェーンの保証から、積極的な脅威ハンティングやOTネットワークの保護に至るまで、この統合的なマッピングにより、規制当局とセキュリティ責任者の双方に対し、追跡可能なデータに基づくレジリエンスの証明を提供します。
OPSWAT 、ファイルフロー、デバイス、ネットワーク全体にわたる可視性を統合することで、運用効率を維持しつつ、進化する脅威への対応態勢を整えながら、あらゆるCAF目標への適合性を示すOPSWAT 。このアプローチは、CAF 4.0への準拠を加速させるだけでなく、規制対象セクター全体における長期的なサイバーレジリエンスを強化します。
セキュリティ責任者は、CAF 4.0 のコンプライアンスにおける複雑さと曖昧さをどのように軽減できるか?
CAF 4.0は、NIS2や英国のレジリエンス法案などの他の規制と重複する成果ベースの構造に基づいて構築されているため、複雑に感じられるかもしれません。セキュリティ責任者としては、証拠の収集と報告を自動化する統合型コンプライアンスツールを活用することで、手作業の負担を最小限に抑えつつ、変化し続ける規制への準拠を維持し、複雑さを軽減することができます。
- 厳格な規制ではなく、セクターごとの重ね合わせを通じて結果を解釈する
- 自動化され、検証可能なデータを用いて証拠収集を標準化する
- 統一された報告体制を活用し、CAF、NIS2、およびレジリエンス法案の要件を統合する
このアプローチにより、複数のフレームワークにわたるコンプライアンス対応が効率化され、CAFの各目標に関するリアルタイムの可視性が維持されるとともに、管理上の負担を軽減しながら、測定可能な進捗状況を示すことができます。
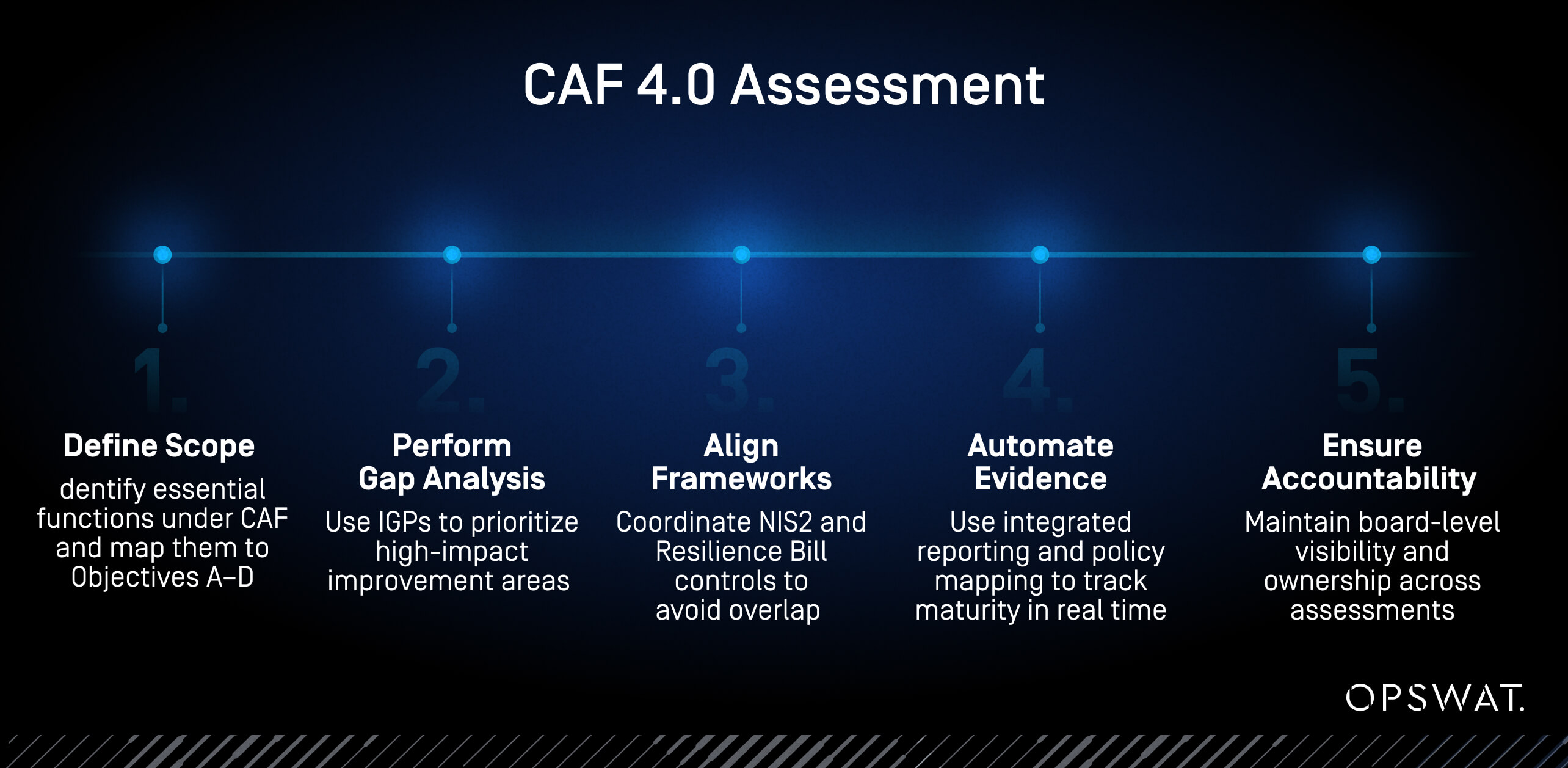
CISOはCAF 4.0評価に備えてどのような対策を講じるべきか?
CISOは、準備態勢の整備、証拠の収集、および規制間の整合性に注力することで、効果的な準備を行うことができます。その目的は、範囲の特定、ギャップ分析、および目標A~Dに沿った証拠の自動収集を通じて、CAF評価を事後対応的なものではなく、予測可能なものにすることです。
- CAFの適用範囲に含まれる必須機能を特定し、それらを4つの主要な目標に照合する
- 更新されたIGPを用いてギャップ分析を実施し、影響の大きい分野を優先順位付けする
- NIS2および英国のレジリエンス法案にセキュリティ対策を適合させ、重複する監査や義務の重複を回避する
- 統合されたコンプライアンス報告機能とポリシーマッピングを活用して、早い段階からデータ収集を自動化し、統制の成熟度をリアルタイムで追跡する
- 評価の間の継続的な可視性を維持するため、取締役会レベルで明確な責任体制を確立する
成果:手作業による準備作業を、継続的な保証とエビデンスに基づくガバナンスに置き換える準備モデル。
CAF監査に向けた証拠を効率的に収集する3つの方法
証拠を効率的に収集することで、CAF監査を単発の取り組みから継続的な保証へと転換することができます。標準化されたテンプレートと自動化されたレポート機能により、組織は成果をリアルタイムで追跡し、一貫性があり検証可能なコンプライアンスの証拠を維持することができます。
- CAF専用のテンプレートと自動データ収集機能を活用し、各管理項目を測定可能な成果と結びつける
- 統合されたコンプライアンス・ビューに証拠を一元化し、CAFの目標に対する進捗状況をリアルタイムで監視する
- 自動化されたレポートから、監査対応可能な簡潔な要約を直接生成し、作成時間とミスを削減します
OPSWAT 、業界横断的な規制の曖昧さOPSWAT
CAF 4.0のセクター別オーバーレイ機能により、各業界は自社の業務リスクに応じて結果を解釈できますが、多くの組織は複数のセクターにまたがって事業を展開しています。「OPSWAT 、統一されたレポートおよび管理アーキテクチャを採用しており、組織は複数の環境にわたって同様のセキュリティ対策を追跡することができます。この一貫性により、多セクターで事業を展開する企業は、証拠や監査を重複させることなく、規制への準拠を維持することができます。
CAF 4.0への準拠を証明するには、どのような証拠や書類が必要ですか?
CAF 4.0では、各管理措置を目標A~Dの成果と結びつける、測定可能かつシステムによって生成された証拠が求められます。管理措置が存在することを示すだけでは不十分です。それらは、長期にわたり効果的かつ一貫して機能していなければなりません。OPSWAT 、自動化されたデータ収集とカスタマイズ可能なレポート機能により、技術的な裏付けと経営層向けの要約の両方を提供することで、このプロセスをOPSWAT
CAF 4.0の要件を満たす3種類の証拠
CAFの証拠の3つの分類
- ポリシーおよびガバナンスに関する文書:リスク登録簿、セキュリティポリシー、インシデント対応計画、およびサプライヤー保証記録
- 運用および技術データ:システムログ、設定ファイル、脆弱性評価、および実稼働環境からのファイルスキャンレポート
- 保証成果物:内部 監査の結果、テスト結果、および「優良事例指標(IGPs)」に準拠した成熟度評価
NCSCのガイダンスでは、証拠は特定の時点での準拠状況ではなく、継続的な運用を裏付けるものでなければならないと強調されています。OPSWAT統合ログ収集機能、監査証跡、および検証レポートにより、各CAFコントロールを、手作業による記録ではなく、システムが生成したデータを用いて検証することが可能になります。
スプレッドシートによるマッピングでコンプライアンス対策を具体化
スプレッドシートによるマッピングでは、各CAF評価項目を具体的な技術的対策と関連付け、証拠が完全か、不完全か、あるいは欠落しているかを示しています。これにより、コンプライアンスの成熟度を即座に把握でき、実行可能な次のステップが明確になります。
CAFの評価結果をOPSWAT統合レポートダッシュボードや監査データと連携させることで、制御状況をリアルタイムで追跡できます。重要インフラ事業者とのパイロット導入において、このアプローチにより、手作業によるレポート作成の負担を50%以上削減すると同時に、監査対応体制を強化することができました。
CAF 4.0における「取締役会提出用報告書」とはどのようなものか?
経営陣への報告には、リスク状況、統制の成熟度、および規制への適合状況に関する明確な要約が必要です。OPSWAT統合レポートダッシュボードは、技術的な指標をビジネスレベルの洞察へと変換した、わかりやすい視覚的な要約を提供します。
業界別のガイダンスがCAF 4.0の導入を加速させる
業界によって直面する運用上のリスクは異なります。そのため、CAF 4.0には、各業界の環境において成果がどのように適用されるかを示す、業界に特化したガイダンスが含まれています。こうした適応策により、組織はより効率的に統制措置を導入し、実際の業務に適合させることができます。OPSWAT 、さまざまな運用環境に合わせて調整可能な自動レポート機能やモジュール式の製品構成を通じて、これをOPSWAT
CI分野におけるCAF 4.0の最重要目標
CAFの優先事項は業界によって異なりますが、すべての業界において、不可欠なサービスを保護するという共通の目標を掲げています。的を絞ったガイダンスと自動化を適切に組み合わせることで、CAF 4.0の導入を加速させると同時に、業界を問わず、管理措置が適切かつ測定可能なものであることを確保します。
エネルギー
システムの耐障害性とOTネットワークのセグメンテーションが鍵となります。OPSWAT MetaDefender およびMetaDefender Drive 、環境の隔離や、接続前のエンドポイントの整合性確認をDrive 。
ヘルスケア
患者データと臨床ワークフローの保護は最優先事項です。MetaDefender Managed File Transfer MetaDefender Managed File Transfer すべてのファイル転送およびアップロードが検証され、クリーンアップされ、追跡可能であることを保証します。
輸送
可用性とデータの完全性がコンプライアンスの基盤となります。OPSWAT統合レポート機能とポリシーベースの転送自動化により、分散システム全体にわたる可視性と制御を維持します。
デジタルインフラ
脅威の検知とセキュアなソフトウェア開発が中核となります。MetaDefender Core Threat Intelligence Core 、継続的な脆弱性評価と予防的な防御Threat Intelligence 。
セクター別のCAF導入テンプレートはありますか?
組織は、OPSWATカスタマイズ可能なダッシュボードとレポート機能を活用し、自社の管理体制を業界固有のCAF成果指標に整合させることができます。これらのツールは、環境を横断した管理状況のリアルタイムな可視化を実現し、チームがCAF 4.0のプラクティスを導入する際に、一貫した基準を適用し、オンボーディングを効率化するのに役立ちます。
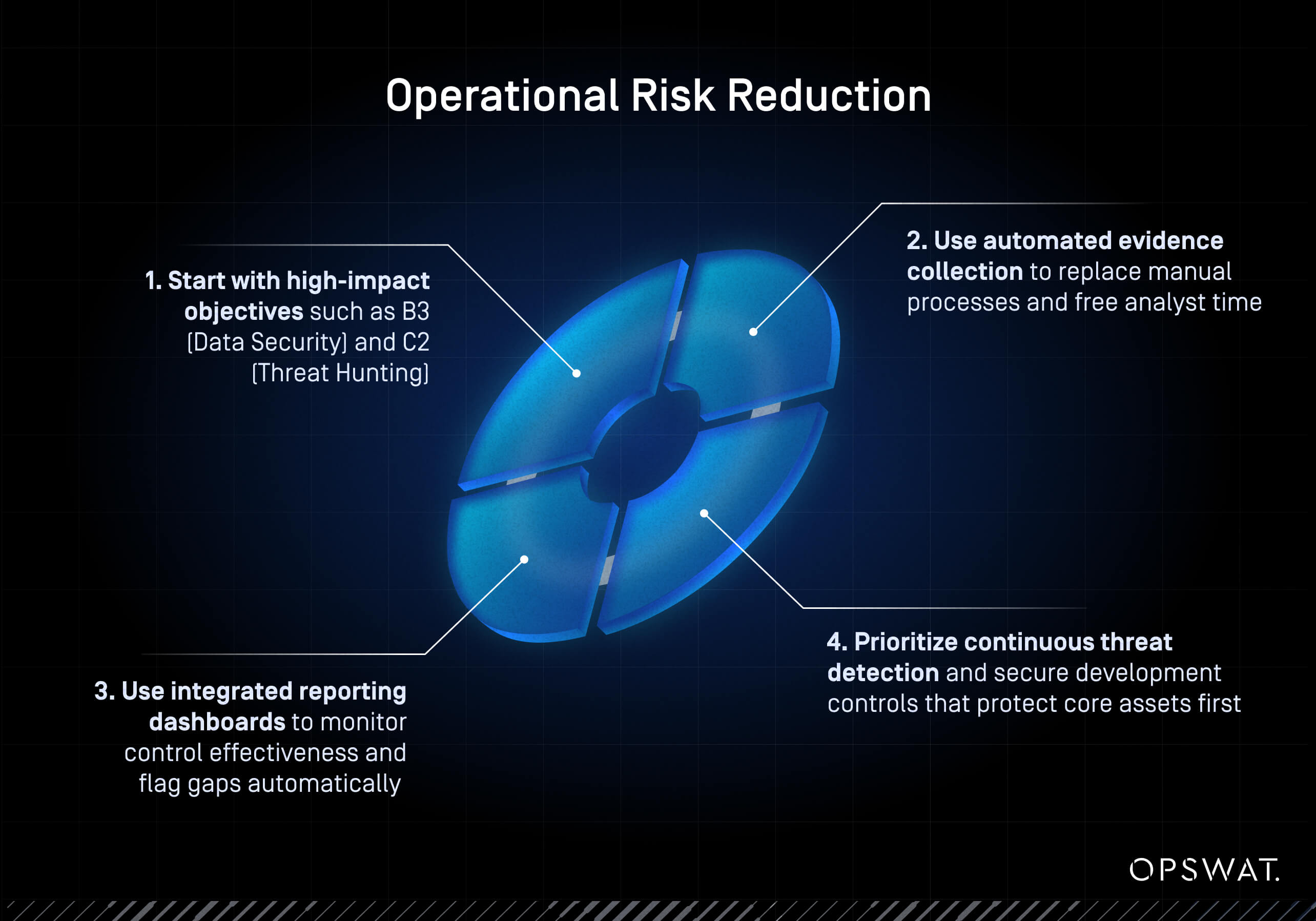
リソースが限られている組織が、最大限のレジリエンスを実現するためにどのように統制措置の優先順位を決定するか
リソースが限られている場合は、運用リスクを最も効果的に低減できる管理策に注力してください。自動化と継続的なインテリジェンスは、リソースの効果を倍増させる役割を果たし、小規模なチームでも大規模な組織と同等のCAF 4.0保証レベルを達成できるようにします。
- まずは 、B3(データセキュリティ)やC2(脅威ハンティング)といった 、影響力の大きい目標から着手してください
- 自動化された証拠収集を活用して手作業のプロセスを置き換え、アナリストの業務負担を軽減する
- 中核となる資産を最優先に保護するため、継続的な脅威検知とセキュア開発の対策に重点を置く
- 統合レポートダッシュボードを使用して、統制の有効性を監視し、不備を自動的に特定する
CAF 4.0が戦略的資産となる理由は何か?
CAF 4.0は、セキュリティパフォーマンスを測定可能なビジネス成果と結びつけることで、コンプライアンスを戦略的な推進力として位置づけます。これにより、組織はサイバーセキュリティの成熟度を定量化し、継続的な保証を実証し、レジリエンスを直接強化する投資に優先順位を付けることが可能になります。OPSWAT自動化されたデータ収集およびレポート機能は、運用データを測定可能なセキュリティ成果と結びつけます。これにより、各制御措置が業務の継続性をどのように支えているかを明確に把握することができます。
「継続的インテリジェンス」は、コンプライアンスと防御体制の将来への備えとなる
リアルタイムのインテリジェンスにより、CAF 4.0への準拠が脅威の状況に合わせて進化し続けます。OPSWATプラットフォームは、ゼロデイ攻撃からAIを活用した攻撃に至るまで、マルウェアエンジンや脅威フィードを自動的に更新します。この継続的な更新サイクルにより、評価の精度が維持され、規制上の証拠が、その時点における組織の真のセキュリティ態勢を確実に反映するようになります。
CAF 4.0 のコンプライアンスや業界固有の要件への対応において、OPSWAT 、信頼性の高い脅威防止技術とコンプライアンス自動化技術を通じて、あらゆるファイル、デバイス、およびデータフローをOPSWAT
OPSWAT にご相談いただき、CAF 4.0への対応を加速させましょう。
よくあるご質問
CAF 4.0では、以前のバージョンと比べてどのような主な変更点がありますか?
CAF 4.0では、チェックリストに基づくコンプライアンスから、測定可能な成果と継続的な保証へと移行します。本フレームワークでは、セキュアなソフトウェア開発要件(A4.b)、AIおよび自動化に関するリスク管理、ならびに正式な脅威ハンティングの原則(C2)が導入されています。また、エネルギー、医療、運輸、デジタルインフラといった各セクター向けのオーバーレイが追加され、NIS2および英国のレジリエンス法案に基づくガバナンス要件が強化されています。
英国の重要インフラ(CNI)組織は、どのようにして「サイバー評価フレームワーク」へのエビデンスに基づく準拠を実証できるでしょうか?
証拠がシステムによって生成され、追跡可能であり、CAFの目標と関連付けられていることを確実にしなければなりません。OPSWAT 、自動ログ記録、統合レポート機能、および各制御措置を測定可能な成果と結びつけるポリシーベースのワークフローを通じて、これOPSWAT 継続的な監視により手作業によるスプレッドシート管理が不要となり、CNI運用担当者はパフォーマンスを確認し、監査可能なコンプライアンスの証拠を提示できるようになります。
取締役会への報告に関するCAF 4.0の要件を満たすために、どのような種類の証拠や文書が必要ですか?
ガバナンス関連の記録(ポリシー、リスク登録簿)、運用データ(ログ、脆弱性レポート)、および保証成果物(監査結果、テスト結果)を総合的に確認する必要があります。OPSWAT これらをOPSWAT 、技術的な指標とCAFの目標を関連付けた簡潔なコンプライアンス要約を作成します。これにより、経営陣は詳細な技術的検証を行うことなく、組織の成熟度とレジリエンスに関するリアルタイムの洞察を得ることができます。
CAFフレームワークは、NIS2やレジリエンス法案といった、今後導入される英国のレジリエンスおよびセキュリティに関する規制とどのように整合しているのでしょうか?
CAF 4.0は、継続的な改善、取締役会の説明責任、および証拠に基づく保証を重視することで、NIS2および英国のレジリエンス法案と密接に連携しています。OPSWATコンプライアンス・マッピングと自動レポート機能により、組織は各規制ごとに個別の監査を維持するのではなく、単一の成果ベースのワークフローを通じて、重複する要件を満たすことができます。
CAF 4.0の下で、脅威ハンティングおよびセキュア開発プロセスを実施するためのベストプラクティスにはどのようなものがありますか?
既知のインジケーターがなくても異常な動作を検知できるツールを活用し、能動的な脅威ハンティング(C2)を導入します。SBOM(Software )の生成や脆弱性スキャンといったセキュア開発の実践(A4.b)を、すべてのリリースに組み込みます。OPSWAT 、MetaDefender 、Core、Threat Intelligenceこれら両OPSWAT 、自動検知、MITRE ATT&CKマッピング、および検証可能なコードの完全性を提供します。
リソースが限られている公共部門の組織は、サイバーレジリエンスを最大化するために、CAF 4.0の統制措置をどのように優先順位付けすべきか?
まずは、運用リスクを最も低減できる影響力の大きい目標(B3 データセキュリティ、C2 脅威ハンティング)に注力してください。証拠収集とファイルフロー保護を自動化することで、アナリストの作業時間を削減します。OPSWAT継続的なインテリジェンスと統合されたコンプライアンスレポート機能により、小規模なチームでも少ないリソースでCAFレベルの保証を維持しつつ、進化する脅威に対応し続けることが可能になります。

